I’ve recently been engaging in some tomfoolery to acquire a list of 51 million Minecraft: Java Edition player UUIDs (out of ~61 million total existing UUIDs). This blog post will explain exactly what I did to make this list.
Abusing the Mojang API with IPv6
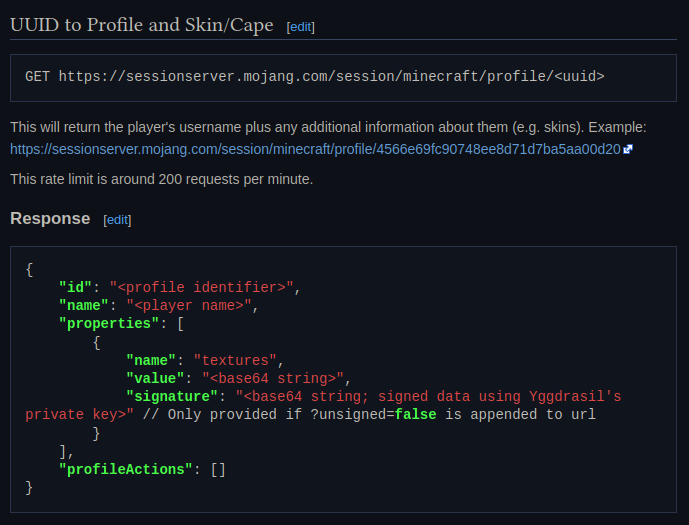
Mojang has an internal API (documented by the community at wiki.
One solution to this problem is IPv6.
Most server hosts will provide you with a /64 subnet (2^64 addresses), so by using a random IPv6 address for each request you can sidestep the ratelimits.
There’s an open-IP_ socket option and randomize the bind address for every socket opened by a program. freebind is great and worked as advertised, but after some testing I noticed that the Mojang API was returning a significant amount of 429 Too Many Requests even though I was using 18 quintillion different IPs.
As it turns out, the Mojang API has some per-
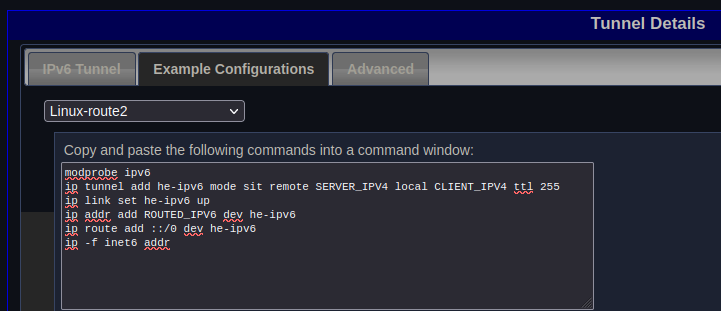
I’m not the first person to do this, and after asking around a bit I was informed that you can use Hurricane Electric’s tunnel broker service to get a /48 (2^80 addresses) for free. Hurricane Electric has a bunch of silly things on their website, but the silly thing I’m using here is tunnelbroker./48, and used their route2 example configuration to add it to my server.
This all worked fine, and I was able to hit the Mojang API at approximately 400 requests per second.
However this is quite slow when you consider the fact that there’s millions of accounts and many more possible username combinations.
The first optimization I did was getting rid of freebind and Rewriting it in Rust™ instead, using raw socket syscalls and a custom Hyper connector.
Basically all my custom connector does is create an AF_ socket, set IPV6_ on it, bind to a random IPv6 address in our subnet, and connect to the destination IP.
At the time there wasn’t any significant speedup, but it did help with an optimization later.
The second “optimization” I did was moving the server and the tunnel IPv6 closer together geographically and to the US, where it got significantly better ping so I could do more concurrent requests at a time.
I also realized that the Mojang API supports HTTP/
Scraping for UUIDs
I already had a few small UUID lists in my hands. I’d previously made a Minecraft server scanner that logged every player on every server, so by gathering up those UUIDs and usernames and feeding them into my program I got a list of about 5 million UUIDs.
Next, I knew about a Hypixel Forums post with 7 million UUIDs that they’d gotten from crawling friends returned by the API, so I checked all of those.
Later, I also found a deleted post on the forums with 14.
![]()
I then made my Mojang API ratelimit evasion tool into a public API for my friends and I to use, and I made it save all valid UUID and username lookups into a SQLite database. It’s hard to estimate how many new UUIDs I got from people using my API, but it’s at least a few thousand.
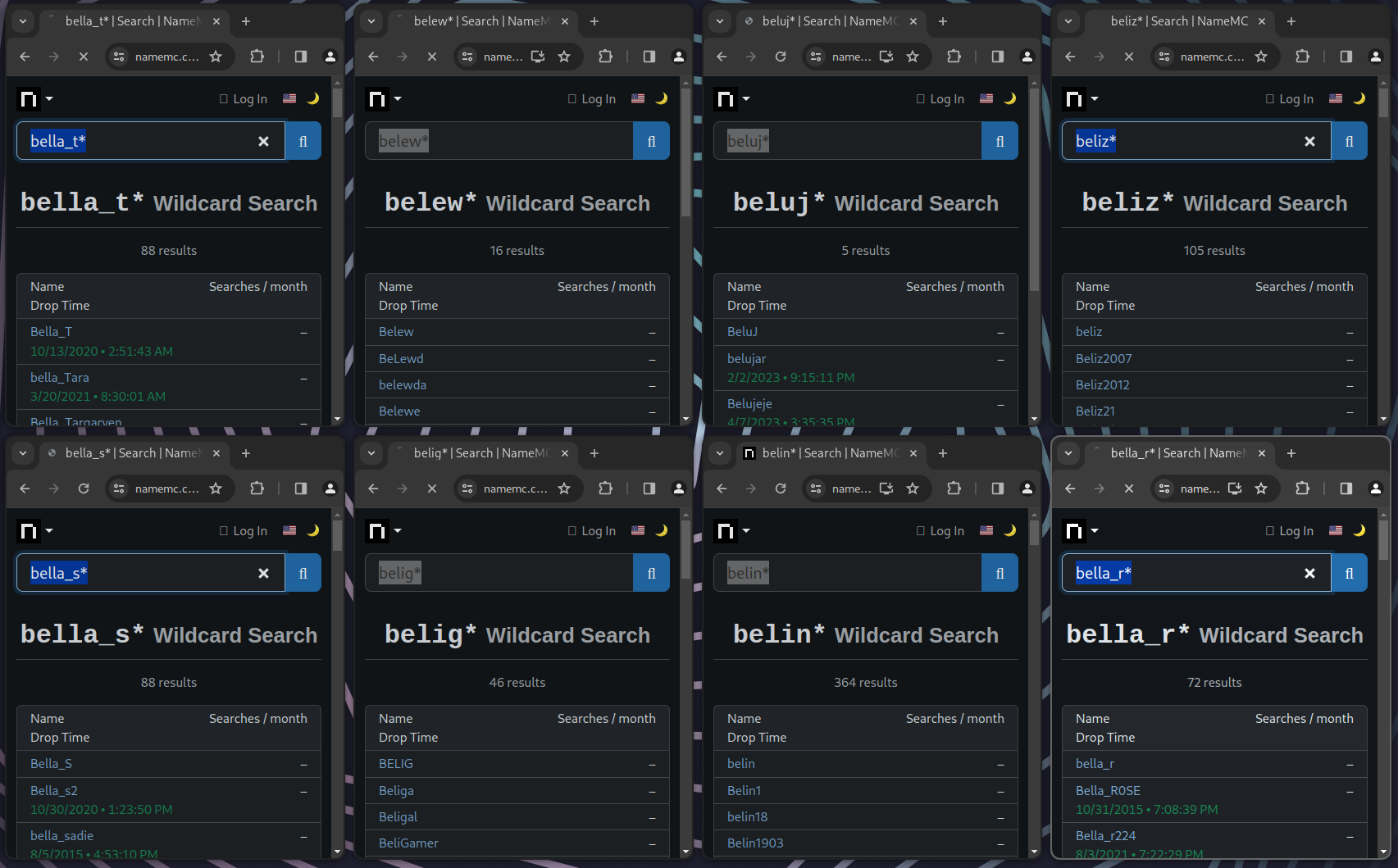
At this point I had 11.abc* you can see every player whose username starts with abc.
NameMC’s existed for a long time, so I figured scraping NameMC’s database by abusing wildcards would be a good way to get a lot of UUIDs.
There were a few things that made this harder though:
- Wildcard queries must have at least 3 characters
- Wildcard searches are limited to 1,000 results
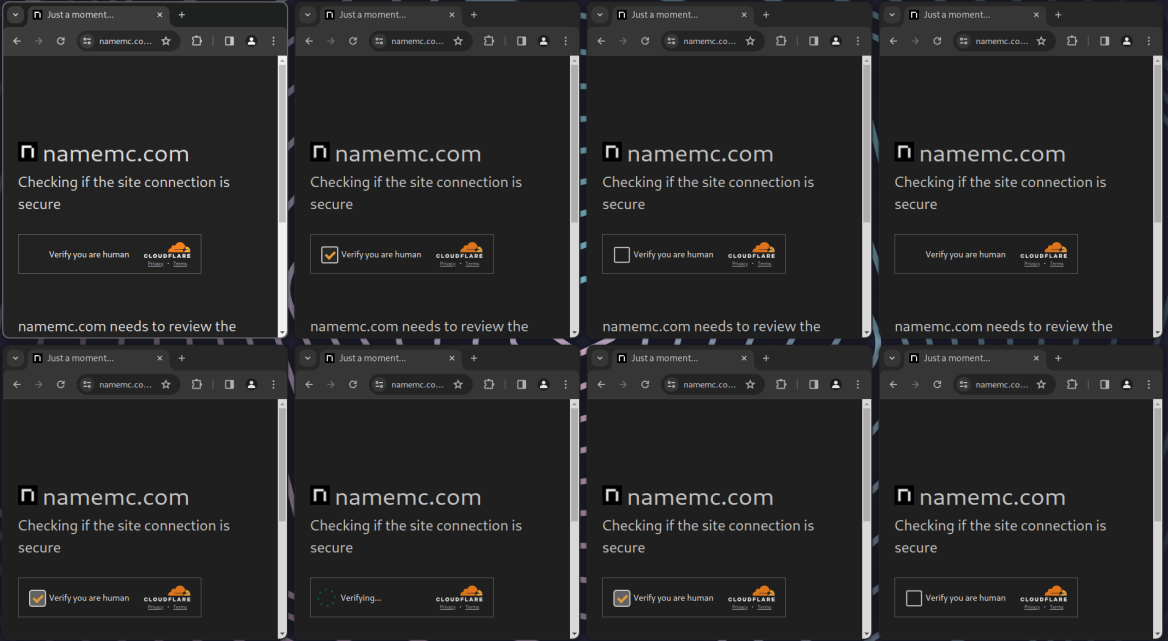
- Cloudflare’s “under attack” mode is permanently enabled, so there’s a captcha every few minutes
- There’s a ratelimit for searching
To work around the first two issues I made a program that finds every possible username by searching like aaa*, aab*, etc, and adding an extra character if the result returned more than 1,000 usernames.
For Cloudflare captchas, I knew they aren’t particularly complex and are solvable with free web scraping libraries.
The first library I tried was undetected-
Now, there’s the issue of ratelimits.
Of course I could use IPv6 once more, but due to the fact that they were Chrome windows on my computer as opposed to basic HTTP requests done by a server, this would be trickier.
I toyed with the idea of using proxies, but after some testing with NameMC I discovered that they check the X- header for ratelimiting, so by randomizing the value of that header I’d never get ratelimited.
Scraping NameMC took a couple days, and I’m well-
Username stuffing
At this point I have pretty much every player who’s played multiplayer at least a few times, so it didn’t seem like there were many more ways to get new players.
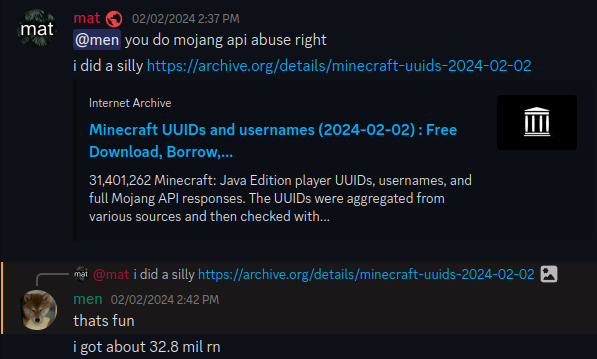
I posted my data on archive.
He told me he’d also scraped NameMC, and was getting new UUIDs by checking usernames from data breaches and making slight variations to existing usernames. Inspired by Northern’s shenanigans, I also began to download some data breaches from questionable sources and stuffing their usernames into the Mojang API. I got many million more from this, but eventually after checking billions of usernames I started to run out of large data breaches to try. One dump I was interested in trying but couldn’t due to its size was the Reddit archives by Pushshift, but luckily my friend cbax was able to download it and provide me with all the usernames of everyone who’s ever posted on Reddit.
Now, I had to try some more creative methods of brute-
One fun brute-
At some point in this process I coincidentally met another UUID harvester named Yuno, after he joined a Discord server about Hypixel SkyBlock programming and claimed to have 55 million UUIDs. 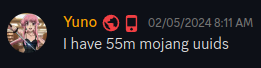
I learned Yuno is in the same group as Northernside, and after we talked a bit he told me he’d also obtained his list from scraping, stuffing usernames from data breaches, and generating usernames. He’s also where the 61 million estimate at the beginning of this blog post comes from; he got it by extrapolating with Hypixel’s lifetime player count.
Epilogue
To help me reach 50,000,000 UUIDs, Northernside and Semisol (who had scraped for Hypixel players a few years ago) also donated their lists to me.
At the time of writing, I have a total of 51,569,249 UUIDs.
I’ve published all the UUIDs (and usernames, and Mojang API responses) I have at archive.
If you’d like to check if you’re in the dataset (you probably are), here’s a convenient widget for searching usernames in my database:
FAQ
The voices
The data will probably be useless to you, but you could use it to reduce the number of requests you have to do to the Mojang API. It could also be used for making user lookup websites like NameMC, or maybe doing something like training AI on usernames or skins or something.
Making archives of user-generated content will usually be controversial since it makes it harder for users to delete their data. However, I believe the harm here is minimal since my dataset doesn't have very much (UUIDs, usernames, skins) and there's other ways of obtaining people's old names anyways (like NameMC, laby.net, etc).
Stats
Here’s some random miscellaneous stats about usernames that I think are interesting:
Length distribution:
Most common words (split by underscores and camelCase):
1. the
2. mr
3. xx
4. king
5. mc
6. man
7. gamer
8. yt
9. big
10. its1. _
2. 1
3. 2
4. 123
5. 3
6. 7
7. 0
8. 12
9. 69
10. 111. 2004
2. 2003
3. 2010
4. 2002
5. 2005
6. 2012
7. 2001
8. 2006
9. 2007
10. 20111. alex
2. shadow
3. max
4. jack
5. chris
6. daniel
7. david
8. nick
9. ghost
10. leo